How AI improves offensive security testing in Pentest-Tools.com
Accurate vulnerability detection helps you move fast without losing trust in results.
That’s why we use AI to improve the stages of offensive security testing where traditional scanning creates noise or gaps.
The result: cleaner signal, better coverage, and less manual work to interpret and report findings.
Here’s how AI works in Pentest-Tools.com.
How you can use our AI-enhanced capabilities today
AI features that summarize findings you already have, inflate your alert queue, and call it intelligence - you've seen them. That’s not how we do things.
We chose to deploy AI where it improves precision or reduces friction - and use deterministic engines where proof matters.
This is what it looks like.
Reduce FPs by 50% with AI-enhanced vulnerability scans
Discover hidden attack surface deep within web apps
Handle complex login forms with AI-assisted authentication
Orchestrate vulnerability scans with our MCP Server
Find hidden resources without filtering out real discoveries
Improve context and triage efficiency with AI-enriched scan results
Find the right plan for your workflow
Each Pentest-Tools.com plan combines capabilities for specific types of security testing workflows. Choose the one that matches your team, customize it with add-ons, and scale as your testing needs grow.
NetSec
[ { "type": "text", "text": "<p>Provides network, cloud, and asset vulnerability assessment.</p>" } ]
WebNetSec
[ { "type": "text", "text": "<p>Goes deeper than NetSec, adding web application, API, and authenticated testing.</p>" } ]
Pentest Suite
[ { "type": "text", "text": "<p>Unlocks the <strong>full workflow</strong>, including automation, exploitation, and professional reporting for full-scope pentests.</p>" } ]
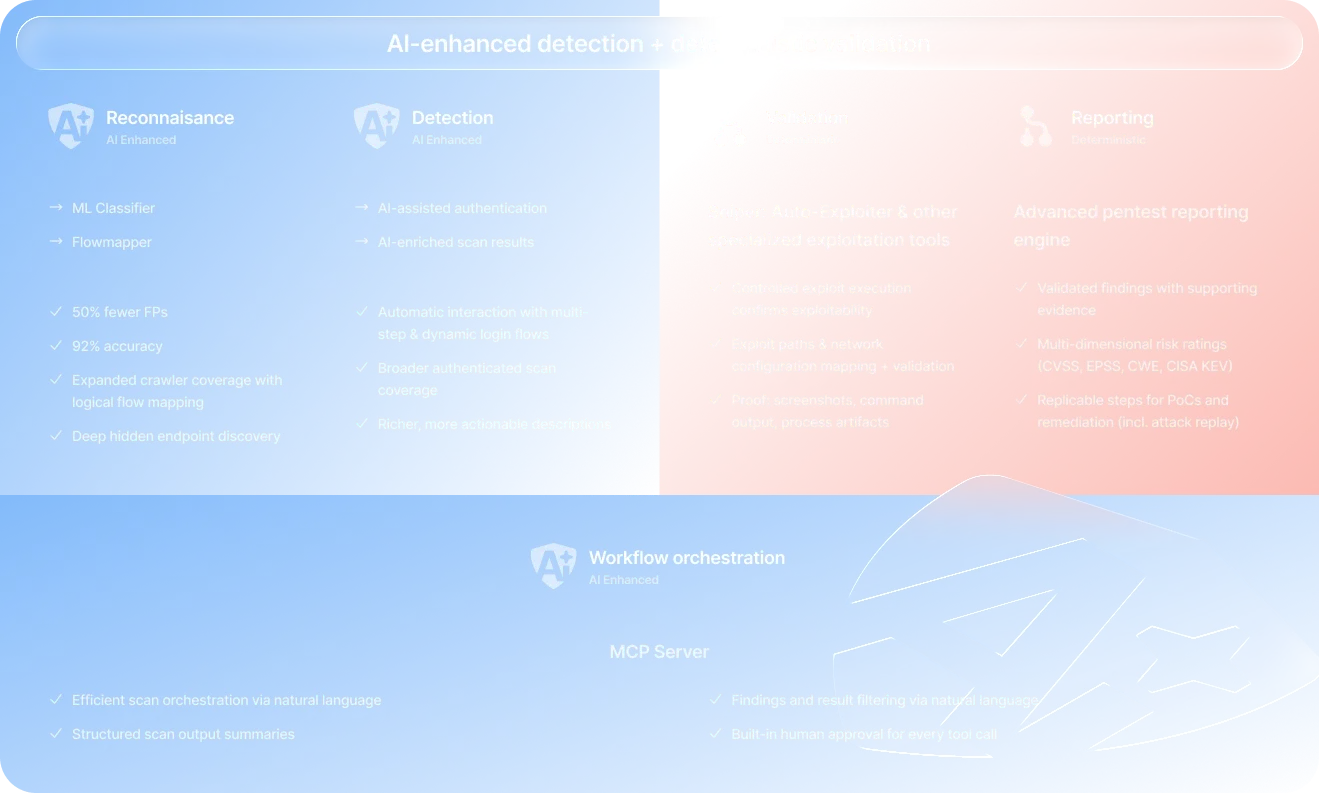
AI improves precision. Validation adds proof.
Pentest-Tools.com combines AI-enhanced detection with deterministic validation to keep your workflow efficient and reliable.
While AI improves the early stages of the pentesting workflow, deterministic engines validate exposure with undeniable proof.
Why we embedded AI in Pentest-Tools.com this way
When adding AI capabilities to the product, our goal was to solve specific operational bottlenecks you face every day:
Scanner noise
[]
Incomplete attack surface visibility
[]
Manual triage overhead
[]
Weak vulnerability validation
[]
That’s why we introduced AI only where it improves precision or reduces friction.
Your core scanning and validation remain deterministic to ensure results are always reproducible and auditable.
What AI doesn’t do in Pentest-Tools.com
Every time you use any of our tools or capabilities, you can be sure we don’t use AI to:
❌ Generate synthetic or "hallucinated" vulnerabilities
❌ Bypass authorization boundaries
❌ Autonomously control scanning engines
❌ Guarantee complete vulnerability coverage.
Instead, AI improves your workflows while you retain full control over every tool and execution.
Who this works best for
Internal security teams
Filter scanner noise automatically, so your team only spends time on truly risky findings.
Maintain credibility with devs by sending them verified exposures with proof.
Validate critical exposures faster and move from detection to remediation in minutes.
MSPs and MSSPs
Scale testing across dozens of clients by automating reconnaissance and high-precision scanning.
Standardize security workflows and deliver consistent, high-quality results across analysts.
Reduce non-billable triage time by automatically discarding FPs.
Security consultants
Validate exploitability instantly during tight engagement windows.
Reduce manual validation effort, letting AI handle complex auth and logical flow mapping.
Deliver defensible reports that clients trust because every finding is backed by verifiable proof.
Trust, privacy, and AI governance
We apply strict governance to all AI-enhanced capabilities to ensure your data remains secure and your results remain yours.
Proprietary infrastructure, not third-party APIs
[ { "type": "text", "text": "<p>We run our proprietary classification models, including the <a href=\"https://pentest-tools.com/features/machine-learning-classifier\">ML Classifier</a>, on our own internal infrastructure. </p><p><br>Where we use hosted language models - for endpoint discovery with the <a href=\"https://pentest-tools.com/website-vulnerability-scanning/discover-hidden-directories-and-files\">URL Fuzzer</a> and AI-assisted authentication with the <a href=\"https://pentest-tools.com/website-vulnerability-scanning/website-scanner\">Website Scanner</a> - we do so on Azure-hosted OpenAI infrastructure <a href=\"https://pentest-tools.com/docs/account-billing/security/where-to-find-policies#ai-data-policy\">under enterprise data terms</a> that contractually prohibit your data from being accessed or used for training.</p>" } ]
Security and isolation
[ { "type": "text", "text": "<p>Our proprietary <a href=\"https://pentest-tools.com/features/machine-learning-classifier\">ML Classifier</a> is hosted on Vast.ai infrastructure. AI-assisted authentication and Flowmapper use GPT-4o, hosted on Azure. Both providers operate under enterprise data terms that contractually prohibit them from accessing or using your data for any purpose beyond delivering the service. You can always find the full details in our <a href=\"https://pentest-tools.com/docs/account-billing/security/where-to-find-policies#ai-data-policy\">AI data policy</a>.</p>" } ]
Zero data retention policy
[ { "type": "text", "text": "<p>We do not log or retain your data for AI-related debugging. There is no retention window for AI processing, ensuring your sensitive scan data exists only as long as the task requires it.</p>" } ]
No model training on customer data
[ { "type": "text", "text": "<p>We do not use your customer data to train external models without your explicit authorization. Our existing models were trained on public data and de-identified, aggregated historical information.</p>" } ]
Classification over generation (no hallucinations)
[ { "type": "text", "text": "<p>Our AI-enhanced capabilities are built to classify data, not invent it. Because our models run inside a rule-based pipeline, a system failure results in a missed classification - not a "hallucinated" or synthetic vulnerability.</p>" } ]
Granular customer controls
[ { "type": "text", "text": "<p>You maintain full control over your environment. You can choose to disable specific AI-assisted enhancements - such as AI-enhanced authentication, ML classification, or Flowmapper - directly from your account settings.</p>" } ]
Human-in-the-loop approvals
[ { "type": "text", "text": "<p><strong>You remain the final authority. </strong>All tool executions triggered through AI-orchestrated workflows (via our <a href=\"https://pentest-tools.com/docs/ai/mcp/overview\">MCP server</a>) require your explicit approval before they run.</p>" } ]
ISO 27001 certified security
[ { "type": "text", "text": "<p>Your confidential results are protected by an independently audited, company-wide Information Security Management System (ISMS). We maintain documented controls, regular risk assessments, and continuous improvements to meet international security standards. <a href=\"https://pentest-tools.com/iso-27001-certificate.pdf\">See our ISO 27001 certificate</a>.</p>" } ]
See how it all comes together
Turn these tools into an in-depth offensive security assessment. We’ve mapped out the most effective workflows to help you get the job done faster.
FAQs about AI in Pentest-Tools.com
What parts of Pentest-Tools.com use AI?
We use AI to improve the most error-prone and noise-heavy stages of the offensive security workflow.
Specifically, AI enhances:
Crawling and attack surface discovery - Flowmapper built into the Website Scanner
Detection precision during web application scanning - ML Classifier built into the Website Scanner
Hidden resource discovery during URL fuzzing - ML Classifier built into the URL Fuzzer
Authentication handling for complex login flows - AI-enhanced authentication built into the Website Scanner
Natural-language workflow orchestration through the MCP server
AI-enriched scan results - built into the Network Scanner
These AI enhancements improve detection signal and operational efficiency during scanning.
What parts of the platform remain deterministic?
To ensure results remain reproducible and auditable, the following components remain deterministic:
Evidence extraction processes
This means Pentest-Tools.com never uses AI to guess whether a vulnerability exists. Instead, deterministic modules confirm exploitability and extract verifiable evidence.
Why doesn’t Pentest-Tools.com rely entirely on AI for vulnerability detection?
AI performs well at recognizing patterns and interpreting complex application behavior. However, vulnerability validation requires deterministic testing to prove exploitability.
Pentest-Tools.com uses AI to improve early-stage detection precision - such as crawling coverage and false-positive reduction - while deterministic engines confirm real exposure through controlled exploit execution.
This architecture improves detection signal while preserving reproducible results.
How does the Machine Learning Classifier reduce false positives?
The ML Classifier analyzes HTTP responses to identify patterns that indicate non-existent pages, namely soft-404 responses.
Instead of relying only on status codes or regex matching, the model evaluates response structure and semantic patterns to distinguish real endpoints from misleading responses.
This reduces scanner noise by up to 50% and improves detection precision to 92% during website scanning.
How does Flowmapper discover hidden attack surface?
Flowmapper analyzes application navigation patterns to identify logical relationships between pages.
This allows the crawler to discover deeper endpoints and hidden paths that traditional crawlers often miss, expanding the attack surface explored during web application scanning.
How does AI help with complex authentication flows?
Modern web applications often use multi-step login flows or dynamic authentication mechanisms that scanners struggle to handle automatically.
Pentest-Tools.com uses AI to analyze login interactions and automatically discover the sequence required to authenticate.
This allows authenticated scans to maintain session context and remain stable throughout the scanning process.
What is the MCP server and how does it work with AI assistants?
The Model Context Protocol (MCP) server allows external AI assistants - such as Claude, ChatGPT Desktop, or Cursor - to interact with Pentest-Tools.com tools through structured commands.
Using natural language, you can:
Trigger deterministic scans
Retrieve findings
Filter results
Generate structured summaries
Every execution requires explicit human approval, and strict JSON-Schema validation ensures predictable and safe tool calls.
How do you prevent “hallucinated” vulnerabilities?
Pentest-Tools.com does not use AI to generate vulnerabilities.
Our AI-enhanced capabilities are designed to classify and interpret data, not invent findings. Because they operate inside rule-based pipelines, a failure results in a missed classification rather than a fabricated vulnerability.
All reported exposures are confirmed by deterministic validation modules that extract real evidence - and every vulnerability in our database is documented in our vulnerability and exploits library.
Is my data used to train AI models?
No. We do not use customer data to train external AI models without explicit authorization.
Our proprietary models were trained using public datasets and de-identified aggregated information.
Do you send sensitive scan data to third-party AI APIs?
Our classification models run on our own internal infrastructure.
This is feature-dependent. Our proprietary ML Classifier runs on our own internal infrastructure and does not send data externally.
For language-model capabilities - endpoint discovery with the URL Fuzzer and AI-assisted authentication with the Website Scanner - we use hosted models on Azure and Vast.ai infrastructure. Both providers operate under enterprise data terms that contractually prohibit them from accessing or using your data for model training or any purpose beyond delivering the service.
You can always find the full details in our AI data policy.
Can I disable AI features?
Yes. Organizations maintain full control over their environment and can disable specific AI-enhanced capabilities - such as Flowmapper, the ML Classifier, or AI-assisted authentication - directly from account settings.
How do AI-enhanced capabilities work in MSP environments?
Pentest-Tools.com supports multi-tenant workflows that allow MSPs to run scans across multiple client environments while maintaining strict isolation between projects.
AI-enhanced capabilities operate independently within each scan environment, helping teams scale testing across clients while reducing manual triage work.
Is Pentest-Tools.com developing autonomous AI pentesting agents?
We are actively researching AI-driven penetration testing workflows and human-supervised offensive agents.
These capabilities are currently experimental and not production features. Our current architecture focuses on improving detection precision while keeping validation deterministic and analyst-controlled.
Is an AI-enhanced vulnerability scanner actually more accurate than a traditional one?
Yes. By combining AI-enhanced detection with deterministic validation, Pentest-Tools.com reduces noise while maintaining reliable results.
For example, the ML Classifier reduces false positives by up to 50%, while the product achieved #1 remote detection accuracy in the Network Vulnerability Scanner benchmark.
How is AI different from traditional vulnerability scanning logic?
Traditional scanners rely heavily on static rules, version detection, and signature matching.
AI allows Pentest-Tools.com to analyze complex patterns in HTTP responses, authentication flows, and application navigation paths that traditional detection logic often misses.
Can AI automate penetration testing completely?
Fully autonomous penetration testing is still in its early stages, and meaningful human judgment remains essential for exploitation decisions and validation.
What's changing is the workload. Security teams today face near-overwhelming volumes of alerts, attack surface, and exploitation attempts. AI can take on more of the repetitive, high-volume work - filtering noise, mapping coverage, handling authentication - so practitioners can focus where it matters.
We're actively researching AI-driven penetration testing workflows and human-supervised offensive agents, and we're excited to contribute to where this is heading. These capabilities are experimental and not yet production features, but they're a direction we're investing in.
How does AI help detect vulnerabilities in web applications?
AI improves vulnerability detection indirectly by improving scan coverage and signal quality.
It helps scanners reach deeper application paths, authenticate reliably, and filter out misleading responses so the underlying detection engines can operate more effectively.
Does AI replace penetration testers?
No. AI in Pentest-Tools.com acts as a force multiplier for security professionals.
It handles repetitive tasks such as filtering false positives, mapping navigation paths, and handling complex authentication flows so analysts can focus on high-value investigation and exploitation.
What makes Pentest-Tools.com different from other AI offensive security tools?
We use AI to improve the most error-prone parts of vulnerability scanning - expanding attack surface discovery, reducing scanner noise, and handling complex authentication flows.
Once the signal is refined, our deterministic engines take over to confirm real exposure through controlled exploitation and forensic evidence extraction.
This architecture allows security teams to move from potential vulnerabilities to verified exposures with proof, while keeping every scan reproducible, auditable, and under analyst control.

